Need Reliable Computer Services: Call (352) 224-3866
Hunting Malware: Why It Takes Several Programs to Clean an Infection
Written by Benjamin Syn on July 13, 2021 Under security
One of my favorite parts of my job is when I get an alert. Our antimalware web interface says something is on one of a clients' workstations. False alarm? Or a genuine threat? Either way, it's go time!
Before I started working in IT, I believed that once antimalware detected a virus, trojan, PUP, etc., it was gone. How wrong I was.
Let's walk through a pretty typical example of a day in the life of hunting malware.
I am Legion
Today, I came in to find the following email from our Remote Monitoring and Management (RMM) software: "The Security Product is Not Installed, The Security Product is Not Active, An infection is found, The Security Product has No Valid License, System Remains Infected for Longer Than 8 hours, The license expires within the next 7 days." There is a LOT to unpack here. Maybe the RMM couldn't find any antimalware at all. Perhaps it's installed but shut down. Maybe the license has expired or is expiring soon.
Or perhaps an infection's been found.
This is likely to sound bad, but I love it when it’s the latter. I can't tell you how much I enjoy hunting malware. And today, I got lucky.
Whenever I get the aforementioned email, my first response is to sign in to the antimalware interface. And sure enough, no false alarm. This computer has been infected! There is malware known as nhsupport.exe on the desktop folder.
I remoted into the computer. Then I immediately sent a message to warn users that this computer has been infected. And then I get to work.
I click on our antimalware in the system tray and run another scan: "Threats Identified – Repair options will be presented when the scan completes." And sure enough, it found nhsupport.exe—in the downloads folder! Uh-oh.
I navigate to the downloads folder for this user and, sure enough, there it is.

So, I decided to bring in some support. I download a second antimalware tool. And I run this tool as well. And sure enough, it finds FOUR instances of malware, including nhsupport.exe—in two other users.
Let's recap:
- According to the first antimalware, User1 has nhsupport.exe is in their downloads.
- According to the second antimalware, User2 has nhsupport.exe in their downloads. Additionally, User2 has two other issues: support.exe and support (1).exe.
- And, there is also a trojan in User3's account (… aller_16783001.exe).
As such, the first antimalware program only found malware in ONE user's folder. Meanwhile, the second antimalware program found malware in TWO other users' folders. Neither program by itself found all the infections.
And this is not a unique phenomenon.
My First Hunt
When I started this job there was one user who always seemed to infect each computer they touch with this one malware: FreeFontPack. Whenever I received ": "The Security Product is Not Installed, …" email for this client, I always knew who it was.
I would throw each antimalware program I could think of at FreeFontPack. And no matter what, the program would say that this malware was quarantined. Until a few days later, when I'd get the alert that FreeFontPack was on another computer.
The problem was that this malware was in a folder that was being redirected from the server. This user signed in to another computer and the malware would be redirected to it. Each new computer that this user touched would get infected from the redirection.
Finally, one day, I put a stop to it. I got on both the computer and the server, and I ran THREE antimalware programs (including Windows Defender).
What surprised me was that I could open up the infected folder and see the file, and then run a malware scan—and it missed FreeFontPack each time. Until I right clicked on this program and scanned with antimalware. Now, when I pointed out the infection to it, this program lit up in red: "Threats Identified!"
Takeaway
Ever since I went overkill on FreeFontPack, there hasn't been another infection detected. The same for nhsupport.exe. But it seems like modern malware requires multiple antimalware to combat it.
As such, here are a few steps to keep in mind to keep your computer safe:
- Install a second antimalware program. Yes, Windows 10 comes with Defender, but we are going to use this as our secondary antimalware program (see below). For our primary antimalware program, I recommend Bitdefender or Malwarebytes.
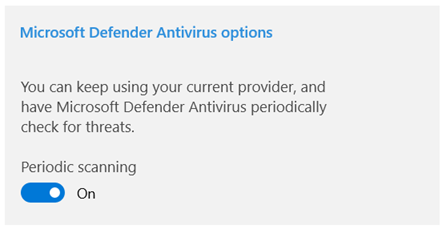
- Enable periodic scanning. Under Settings, Update & Security, Windows Security, click on Virus & threat protection. At the very bottom, click on the blue words Microsoft Defender Antivirus options and move the Periodic scanning slider to On.
- Download backup antimalware programs. Here I highly recommend McAfee Stinger and Emsisoft Emergency Kit. Instead of being for everyday use, these are portable backups. Both of these have Portable App options that you can use on a flash drive.
I know that seems like we're trying to kill a bug with a sledgehammer. The problem is, as you saw above, it isn't just one bug. What's the adage about cockroaches? If you see one, there are dozens more hidden in the walls. The same here.
It's the same when hunting malware. If one of your programs detects one, there's likely more this antimalware can't see. As such, be prepared to bring out the big guns.
Or you can leave it to the professionals. Check out our Managed Services for more information. We love hunting malware and have all kinds of toys to call upon when a computer gets an infection.
Call Us: (352) 224-3866